As more and more businesses go digital, data security has become paramount. It is an extremely important aspect of data management and must not be overlooked as it can lead to issues, such as compromised data security, unexpected losses, and damaged reputation.
In the last few years, data breaches have become a much bigger problem than ever. According to a report by IBM, in 2022, the global average total cost of data breaches reached an all-time high at $4.35 million, representing a hike of 12.7% as compared to 2020.
Clearly, it is inevitable for businesses to make sure they have solutions in place to prevent their systems and applications from being attacked by unauthorized parties. One of the ways to keep confidential data safe is through authentication and authorization.
Let’s discuss them in detail:
Authentication Vs Authorization
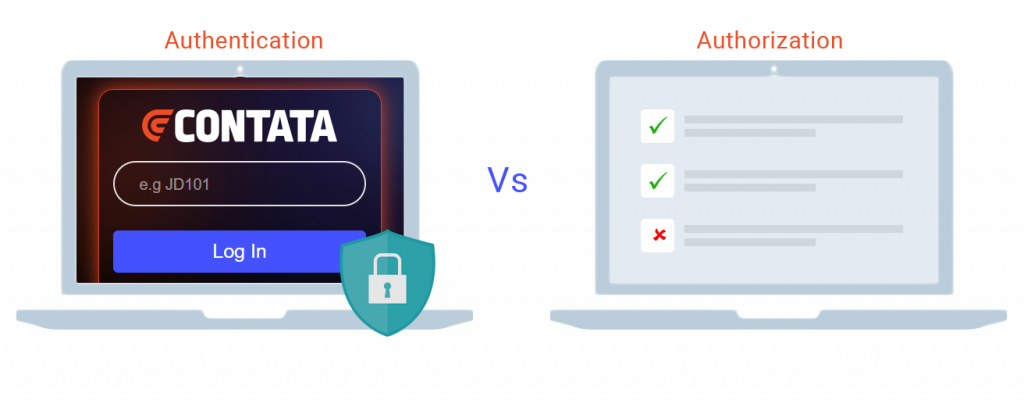
The terms authentication and authorization are often used interchangeably; however, they both serve different purposes. While authentication aims to verify a user’s identity, authorization verifies what the user can access, such as applications, files, photos, etc.
Instead of being used separately, authentication and authorization are generally used in combination to add more security to company applications and prevent them from cyberattacks. Authentication is the first step towards data security followed by authorization. Below are a few examples to explain how they work together:
- In a company, employees must first “authenticate” their identity through the company’s network to access data. After successful authentication, the system determines what information the employees are “authorized” to access and only displays that. The displayed information would vary depending on whether the employee is an executive or a manager.
- When a customer wants to access their bank account through the bank’s mobile app, they are required to “authenticate” their identity with a user ID & password, or biometrics, such as fingerprint or face ID. Once authenticated, the bank’s system determines the information the customer is “authorized” to access—based on their account type and permissions—and only displays that.
- A drilling contractor wanting to access a shared platform to manage drilling operations is required to first “authenticate” their identity through security tokens or biometric information. Once authenticated, the platform determines the information the contractor is “authorized” to access, such as well logs, and only displays that.
- The staff looking to access a patient’s EHR to review their medical history, lab results, or prescriptions, needs to “authenticate” their identity through smart card or biometrics. The system will determine whether partial or full information must be displayed to the user based on the authentication. The displayed information would vary depending on whether the user is a doctor or a nurse.
Depending on the level of security required and the specific needs of a business or application, the choice of authentication and authorization would vary. Below are some of the commonly used methods:
Authentication Methods
- Password-based – The most common type of authentication is password-based where a user is required to submit their user ID and password to gain access to a system or application.
- 2FA – The second method is two-factor authentication, also known as 2FA, where the user is required to enter a password, as well as a one-time password (OTP), which is sent to the user via SMS or a mobile app. The OTP needs to be submitted, usually within 30 seconds, or it expires, and a new OTP needs to be generated. The method allows for double verification.
- MFA – The next authentication method is multi-factor authentication, also known as MFA, which is basically going one step ahead of 2FA. In addition to a password and a one-time password, biometric information, such as fingerprint, face ID, voice recognition, or iris scan, are also required for access. This authentication provides even more security than 2FA.
- Token-based– Another method is token-based authentication which requires the use of a physical token, such as a smart card or USB key, to access a system or application.
Authorization Methods
- Role-based access control (RBAC): In RBAC, the authorization is based on the user’s role within an organization or system. The authorization of a vice president would be different from an operation or production Manager.
- Attribute-based access control (ABAC): In this method, the authorization is based on the attributes of the subject, resource, action, and environment involved in an access event.
- Rule-based access control: In rule-based access control, the authorization is based on a set of rules that determine who can take what actions. For example, a rule may be established that only seniors in the IT department are authorized to access a particular resource.
- Mandatory access control (MAC): In MAC, the authorization to access resources is determined by a central authority, which is again based on predefined data security policies.
- Discretionary access control (DAC): In DAC, the authorization is based on the owner’s discretion. Here, the owner decides who will access what and how much.
Authorization & Authentication Mechanisms: OAuth, OpenID Connect, & SAML
OAuth, SAML, and OpenID Connect are different data security mechanisms based on authentication and authorization in web applications. While OAuth is used for access authorization, SAML and OpenID Connect are used for user authentication. Depending on the requirements, a company may use one or all of these data security protocols to keep their data safe. OAuth can be used for API access, OpenID Connect for user authentication, and SAML for single sign-on enterprise applications. Let’s discuss them in detail:
OAuth
OAuth or Open Authorization is an open authorization framework that provides secure authorization to third-party services—in web, mobile, and desktop applications—to access protected resources on the user’s account. The authorization server provides access tokens to third parties without exposing user credentials, such as ID and Password. The four main parties involved in the process include the resource owner, client, authorization server, and resource server. Initially designed for social networking sites, OAuth has now become a standard for authorization and is commonly used for API access in web applications.
OAuth 2.0 vs OAuth 1.0
Launched in December 2007, OAuth 1.0 is an older version of OAuth that first introduced the digital signature-based system for access delegation. Although strong and resilient, OAuth 1.0 had issues that challenged its implementation for many developers. There wasn’t enough support for non-browser applications, the sign-in was complex, and the access tokens were short-lived.
Launched in October 2012, OAuth 2.0 is a complete rewrite of OAuth 1.0. It solved most of the problems OAuth 1.0 presented and is much easier to implement. Most importantly, OAuth 2.0 requires only one security token and once that token has been generated, there is no need for additional signatures to make API calls.
OpenID Connect
OpenID Connect or OIDC is an open authentication protocol that provides a standardized way for users to authenticate themselves across different web services and applications using their existing accounts. OpenID Connect works as a complementary protocol to the OAuth 2.0 framework and adds an extra layer of security by using JSON Web Token (JWT) in REST-like format to standardize areas that are left optional by OAuth 2.0. Optional features include encryption of identity data and session management. The four main parties involved in the process include the OpenID provider (OP), the end-user, the relying party (RP), and the user agent.
OpenID Connect vs OpenID 2.0
Although OpenID Connect is quite similar to OpenID 2.0 when it comes to functionality, it performs tasks in a way that is more API-friendly and usable by native and mobile apps. Another difference is OpenID 2.0 requires extensions to integrate OpenID 1.0 and OAuth 1.0, whereas OpenID Connect is already integrated with the two security protocols.
SAML
Primarily used for web browser single sign-on (SSO), SAML or Security Assertion Markup Language is an XML-based markup and open protocol that is designed to exchange authentication and authorization data between the user, identity provider (IdP), and service provider (SP). The user is the person who wants to access a service or application. Identity provider is the service that authenticates the user and provides an assertion containing information about the user to the service provider. The service provider is the service that hosts the protected resources that a user wants to access.
So far, three versions of SAML have been released: SAML 1.0, SAML 1.1, and SAML 2.0. The latest version SAML 2.0 is built on top of SAML 1.1 specifications, however, it is not backward compatible. Because SAML 2.0 provides a mechanism for federated identity. It is often used for authorization in enterprise and government applications.
OAuth, OpenID Connect, & SAML: Comparison with Pros & Cons
| Protocol | Type | Pros | Cons |
| Oauth | Authorization | No need to share credentials with third-party apps. Uses access tokens instead of passwords. Access can be granted for limited sco pe and duration. The client app uses SSL (Secure Sockets Layer) to securely communicate with the authorization server. |
Writing authorization with QAuth can be complex. Interoperability can be a challenge in implementation. Loose implementation can lead to security issues. Prevents users from freely controlling their data. |
OpenID Connect |
Authentication |
Includes advantages of OAuth 2.0. Single sign-on (SSO) capabilities API friendly, and supports single-page, native, and mobile applications. Easier to implement than SAML Can also provide basic user information with an access token. |
The user needs an account with OpenID providers. The OpenID providers can track the user’s habits as they receive all the authentication requests. |
SAML |
Authentication |
SAML abstracts security framework from the platform, making security independent of application logic. Single point of authentication at the secure identity provider Single sign-on (SSO) capabilities |
Only provides SSO for web applications with a server backend. No interoperability to support SPAs or mobile apps. XML vulnerabilities Complex implementation |
Final Thought
Authentication and authorization protocols, such as OAuth, OpenID Connect, and SAML are a great way for businesses to prevent their confidential data from getting exposed to unauthorized parties. However, deciding the right security infrastructure and framework for web applications or services can be a challenge. Knowing when to use what is an important step towards securing your organization’s data.
How Contata can help
Contata is a data science and application development company with over 20+ years of experience. We provide secure product engineering solutions to businesses, offering peace of mind and ensuring that their data is secure and protected with the right protocols. We offer top-notch support for distributed/enterprise application & product development which includes optimal security mechanisms (such as OAuth, OpenID Connect, and SAML) along with complete software development life-cycle support to IT administrators with a broad range of features that they can use to monitor and secure access to corporate resources.
Get in touch with one of our experts to know how we help you to keep your data secure.
